2023 Activities Summary of SectorD groups (ENG)
Activity of SectorD Group
In 2023, hacking activities by a total of 12 SectorD subgroups were identified. The groups primarily conducted hacking activities targeting countries under political dispute with the government that supports the groups. Recently, SectorD groups have been analyzed to be collecting advanced information such as political and diplomatic activities of individuals and governments against the government that supports the groups.
Among the SectorD hacking groups, activities by a total of 12 hacking groups were identified in 2023, with the activity of SectorD01 group being the most prominent.
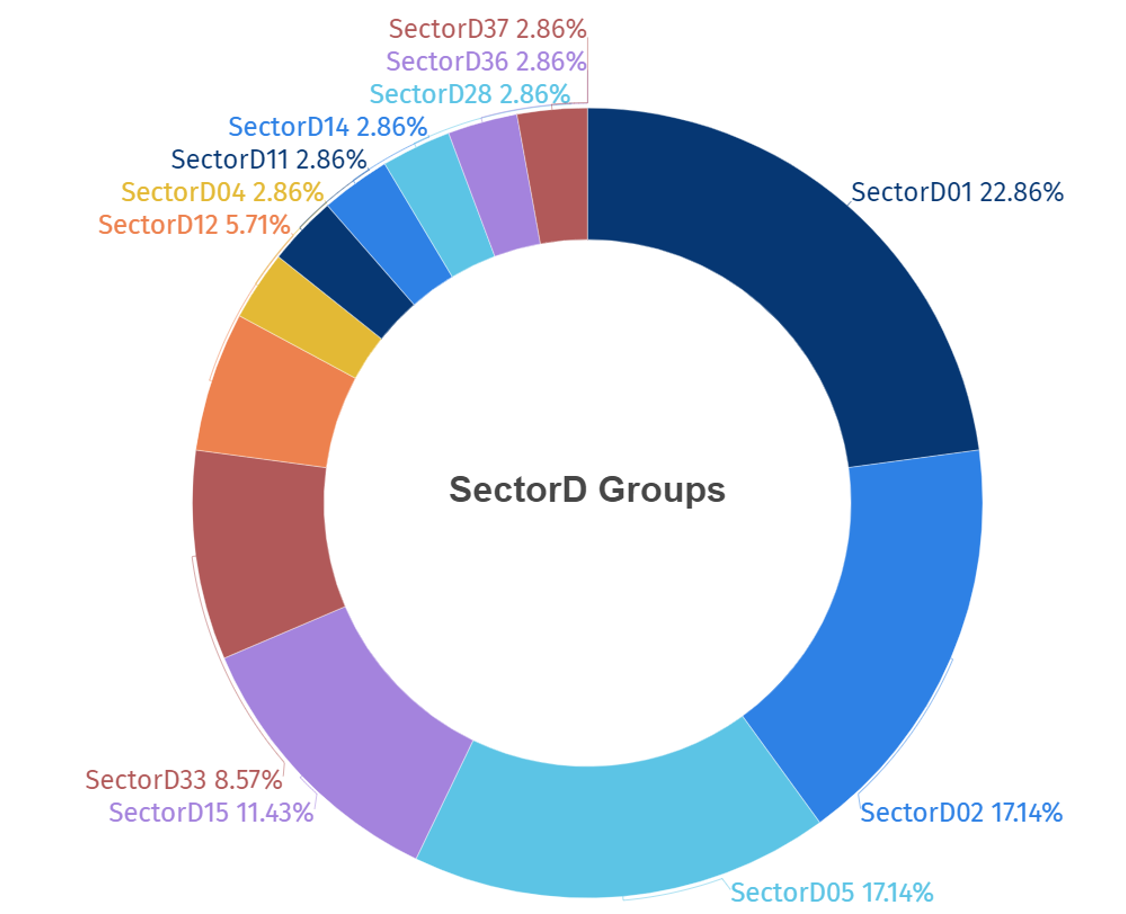
[Figure 1: Statistics of Activities of SectorD Groups identified in 2023]
SectorD hacking groups identified in 2023 carried out the highest number of attacks on workers and systems in government agencies, followed by defense and transportation sectors.

[Figure 2: Statistics of Industries Targeted in 2023]
The following map illustrates the countries targeted by SectorD groups in 2023, with darker shades of red indicating higher frequencies of attacks. This shows that SectorD Group conducted the most hacking activities against Ukraine, followed by the United States.

[Figure 3: Countries Targeted by SectorD Groups in 2023]
INITIAL ACCESS Route of SectorD Group
Among the initial access routes used by SectorD groups, distributing spear phishing with malicious link was found to be the primary access route used in 2023.
Spear phishing attacks are social engineering attacks targeting specific individuals or organizations. Through malicious links, attackers induce targets to input their credentials or execute malware.
The groups disguise themselves as trusted contacts or credible individuals to induce the target to execute malicious links or attachments, making spear phishing the most commonly utilized method with its high likelihood of successful initial access.
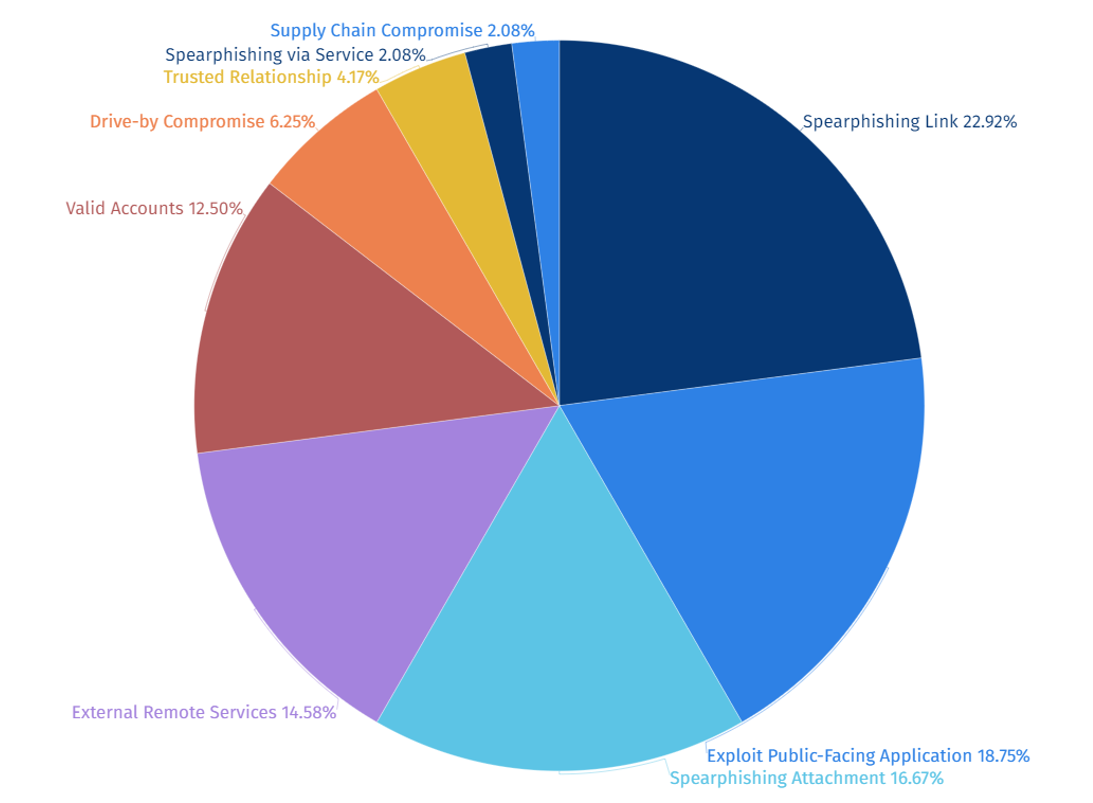
[Figure 4: Statistics of Initial Access Routes used by SectorD Groups]
Vulnerabilities Exploited by SectorD Group
Among the top 5 vulnerabilities exploited by SectorD groups in 2023, CVE-2022-47966 (a remote code execution vulnerability (RCE) in Zoho ManageEngine) was found to be the most frequently used.
Hacking groups install malware or software on target systems to achieve their goals, with remote code execution (RCE) vulnerabilities being the most commonly exploited during this process.
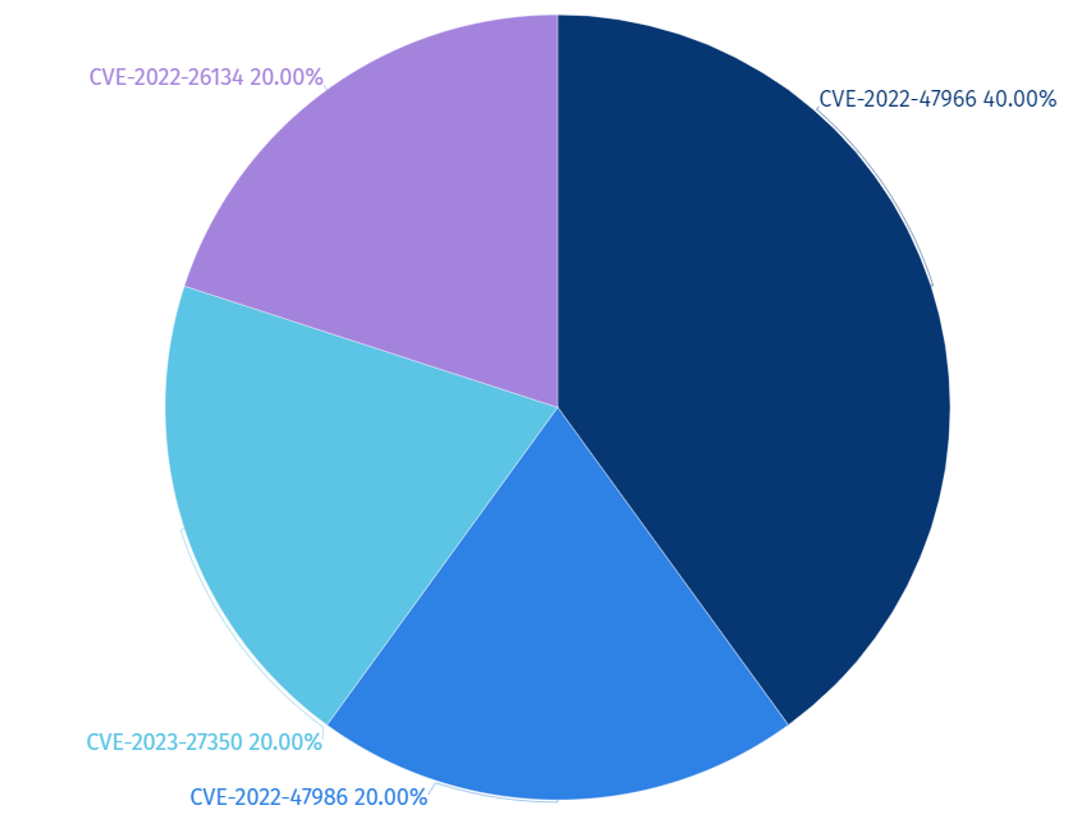
[Figure 5: Statistics of Top 5 Vulnerabilities Exploited by SectorD Group in 2023]
|
Vulnerability |
Classification |
Target System |
|
CVE-2022-47966 |
Remote Code Execution Vulnerability |
Zoho ManageEngine |
|
CVE-2022-47986 |
Code Execution Vulnerability | IBM Aspera Faspex |
|
CVE-2023-27350 |
Improper Access Control Vulnerability |
PaperCut MF/NG |
| CVE-2022-26134 | Remote Code Execution Vulnerability |
Atlassian Confluence Server and Data Center |
[Table 1: Top 5 Vulnerabilities Exploited by SectorD Group in 2023]
SectorD Attack Target Systems Statistics
Software vulnerabilities are typically categorized into server and client types. Hacking groups, strategically positioned at the heart of networks, exploit vulnerabilities within server systems to facilitate further attacks on internal networks.
Among the top 5 attack target systems by SectorD groups in 2023, the business management software product “Zoho ManageEngine” was the most frequently targeted system. This is believed to be aimed at establishing a foothold to infiltrate internal organizational systems and for the purpose of exfiltrating high-value information, thus making server-type systems the primary target of the attacks.
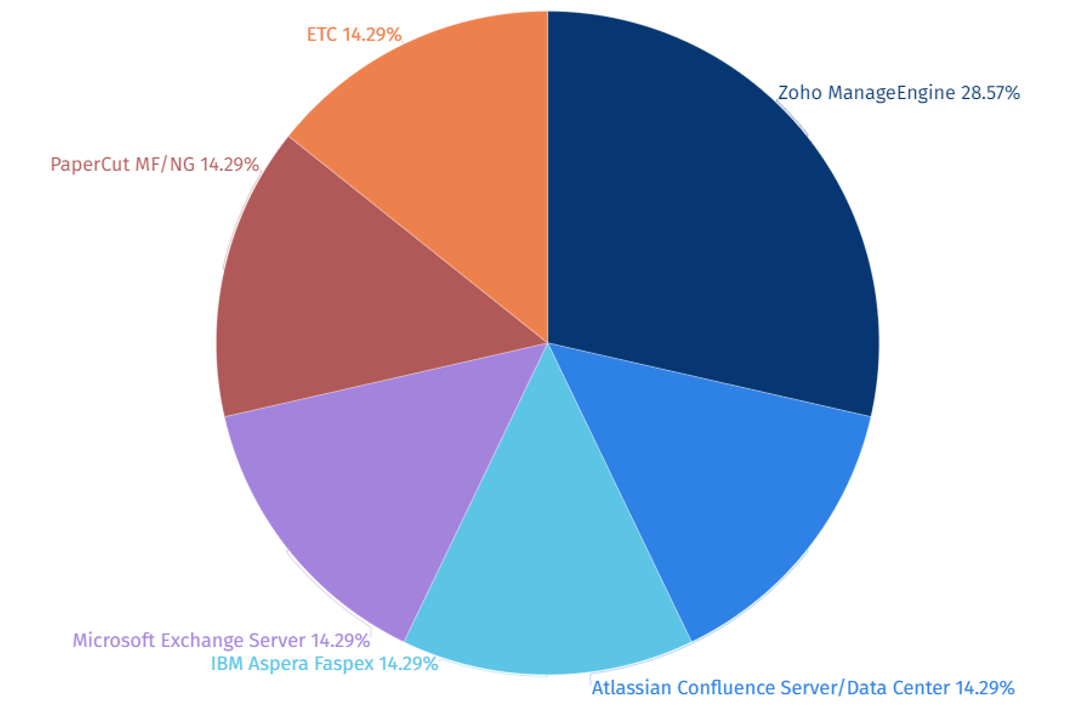
[Figure 6: Statistics of Top 5 Attack Target Systems by SectorD Group in 2023]
Open Source and Freeware Tools Utilized by SectorD Group
Among the top 5 open source and freeware tools utilized by SectorD groups in 2023, the remote access program ‘Putty’ was identified as the most frequently used tool. It has been determined that these groups controlled victim systems remotely using remote access programs like ‘Putty’.
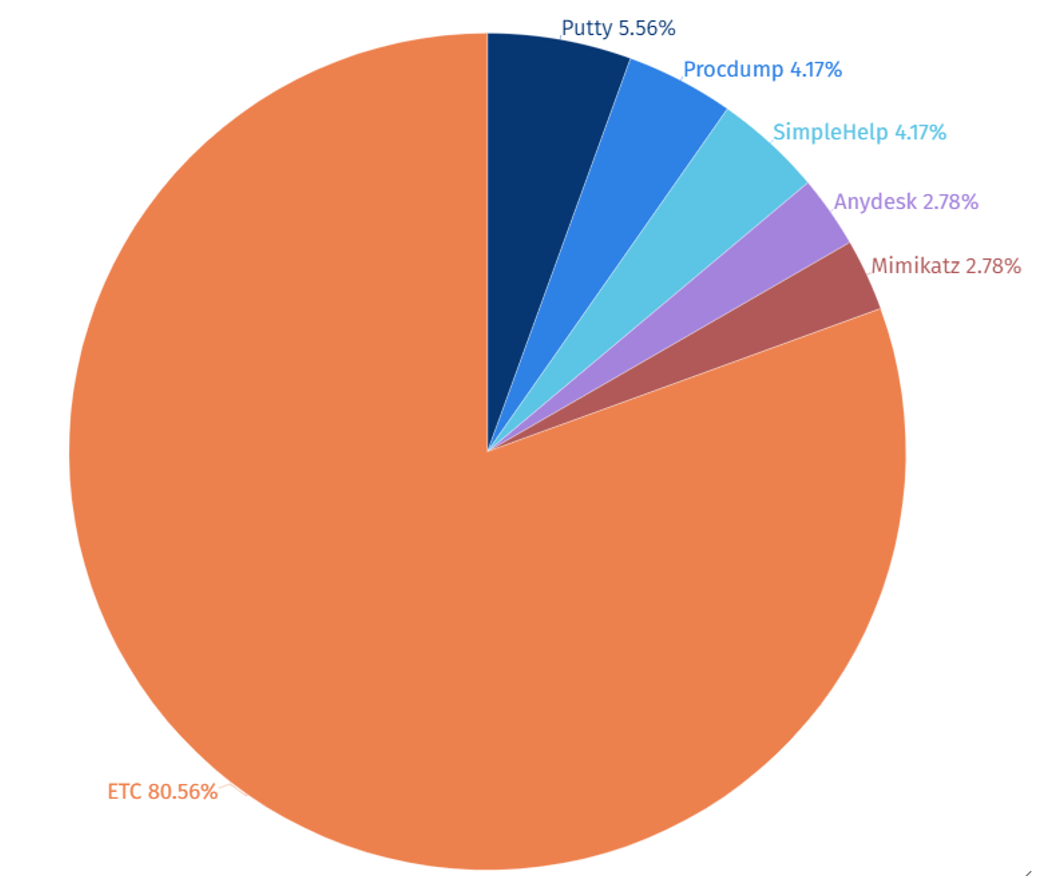
[Figure 7: Statistics of Top 5 Open Source and Freeware Tool used by SectorD Group in 2023]
|
Tool Name |
Function |
|
Putty |
Remote Control Program |
|
Procdump |
Process Dump Tool |
|
SimpleHelp |
Remote Control Program |
|
Anydesk |
Remote Control Program |
|
Mimikatz |
Windows Credential Information Collection Tool |
[Table 2: Top 5 Open Source and Freeware Tool used by SectorD Group in 2023]
The full report detailing each event together with IoCs (Indicators of Compromise) and recommendations is available to existing NSHC ThreatRecon customers. For more information, please contact service@nshc.net.
